Anonymizing software solution that can be used to prevent websites from tracking your activity or to connect to webpages that are usually blocked in your area. #Anonymize browsing #Browser anonymizer #Stealth browsing #Anonymize #Stealth #Anonymizer
Privacy is a very important issue these days now that everyone is monitoring and analyzing internet traffic. As a result, the use of a VPN to mask your online activity is quite popular.
Initially developed as a secure communication tool for the US Naval Research Laboratory, the Tor project has become a standard whenever you need to share information without compromising your identity.
Tor can be used to prevent websites from tracking your activity or to connect to webpages that are usually blocked in your area. You can publish websites without providing their location.
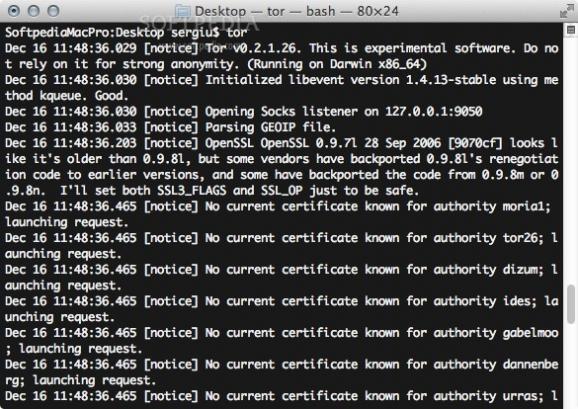
Tor can be installed and accessed via the command line, although the developers provide a Tor Browser Bundle that is easier to use and set up. The drawback is that you remain protected only when you are using the Tor browser.
However, the Tor command line version is more efficient if you need to host certain services or if you want to be a volunteer and relay traffic to other users.
Start by installing Homebrew and then use the package manager to install Tor. Make sure that you also have Xcode with its development tools installed before proceeding.
Tor can be used with any application as long as you configure it properly and make sure the application’s internet connection goes through the Tor network.
This means that you must set up the Tor client as the SOCKS proxy. If you are interested in application level anonymity, you can read the documentation provided by the Tor development team HERE.
Tor is a very efficient tool if you need to anonymize your internet traffic: by going through the Tor network, whoever is tracking your activity does not have access to the data header, which can disclose the package size, timing, the source and destination and so on.
Tor is essential whenever you want to communicate safely and maintain your privacy over the internet, no matter where you are, as long as it is configured correctly.
Download Hubs
Tor is part of these download collections: Hide IP
What's new in Tor 0.4.8.11:
- Minor feature (authority):
- Reject 0.4.7.x series at the authority level. Closes ticket 40896.
- Minor feature (dirauth, tor26):
Tor 0.4.8.11
add to watchlist add to download basket send us an update REPORT- runs on:
- macOS (-)
- file size:
- 9.7 MB
- filename:
- tor-0.4.8.11.tar.gz
- main category:
- Security
- developer:
- visit homepage
calibre
Bitdefender Antivirus Free
Zoom Client
7-Zip
4k Video Downloader
Windows Sandbox Launcher
Context Menu Manager
IrfanView
Microsoft Teams
ShareX
- IrfanView
- Microsoft Teams
- ShareX
- calibre
- Bitdefender Antivirus Free
- Zoom Client
- 7-Zip
- 4k Video Downloader
- Windows Sandbox Launcher
- Context Menu Manager