A powerful, versatile and user-oriented utility that enables you to remotely take control of other computers, regardless of their operating system. #VNC server #VNC viewer #Remote control #VNC #Remote #Administration
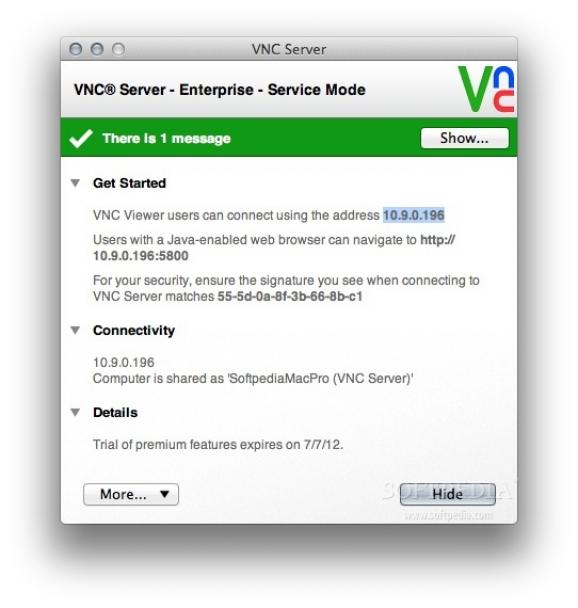
RealVNC Server is a practical and easy-to-use cross-platform application that enables you to control your devices from various remote locations with ease.
VNC, short for Virtual Network Computing, is a straightforward graphical desktop sharing system that helps you control another computer via the Remote Frame Buffer protocol (RFB).
VNC is capable to transmit the keyboard and mouse events from one computer to another over any given network.
With the app's help, you can easily establish connections between computers of different operating systems, from macOS and Windows to Linux and UNIX.
What is more, the connection between computers is protected by an encrypted password that provide protection against connection snooping, man-in-the-middle attacks, packet-tampering and more.
Thanks to the seamless integration with the system authentication system, you can use your own credentials of the user accounts to connect to another computer.
Also, all your connections are encrypted using 128-bit or 256-bit AES, a fact that translates into high performance encryption and protection.
You can print files using the printers connected to the remote computer, transfer files between devices, and chat with the host computer user or other users connected at the same time.
In order to use RealVNC Server, you first have to install the app on the computer you want to control and run RealVNC Viewer on the Mac you want to control from.
By accessing VNC’s Options window, you can apply IP filters, change the connection port, customize the security settings, enable the guest access, share connected printers and enable or disable keyboard and mouse input, the clipboard share feature, chat and file transfer function.
What's new in RealVNC Server 7.11.0:
- NEW: RealVNC Server for macOS now supports use of Apple’s ScreenCaptureKit API for desktop capture, on macOS 12.3 and later.
- NEW: RealVNC Server can now prevent the built-in Windows On-Screen Keyboard from being displayed to connected RealVNC Viewers. This can be enabled using the new Expert parameter HideOSKWindow.
RealVNC Server 7.11.0
add to watchlist add to download basket send us an update REPORT- runs on:
- macOS 13.0 or later (Universal Binary)
- file size:
- 17.8 MB
- filename:
- VNC-Server-7.11.0-MacOSX-universal.pkg
- main category:
- Network/Admin
- developer:
- visit homepage
Context Menu Manager
ShareX
IrfanView
Microsoft Teams
calibre
Zoom Client
7-Zip
Windows Sandbox Launcher
4k Video Downloader
Bitdefender Antivirus Free
- Windows Sandbox Launcher
- 4k Video Downloader
- Bitdefender Antivirus Free
- Context Menu Manager
- ShareX
- IrfanView
- Microsoft Teams
- calibre
- Zoom Client
- 7-Zip