Open source project that delivers access to the SSH protocol and features tools that can help you secure remote file transfers or remote logins. #Ssh protocol #Network conectivity #Encrypt traffic #Ssh #Protocol #Connectivity
OpenSSH is an open source project that provides access to a suite of tools that can help you protect your traffic by relying on the SSH protocol and encryption capabilities.
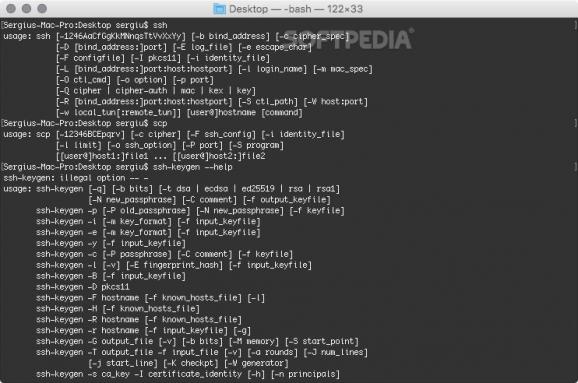
The OpenSSH software collection can handle remote connections via SSH, SCP, and SFTP, and provides key management tools (SSH- Keygen, SSH-Keyscan, SSH-Keysign, and SSH-Add).
Moreover, OpenSSH features additional utilities for dealing with various services: SSHD, SFTP-Server, and the SSH-Agent. Note that all these tools can be accessed only via the command line.
The OpenSSH project tries to make it possible for anyone to use the SSH protocol in order to make their online activity as safe as possible. The protocol mainly delivers encryption capabilities for remote login or remote file transfers.
Note that OpenSSH also includes SFTP support both for the client and server side and that it can deal with both SSH1 and SSH2 protocols.
Thanks to the interoperability approach, OpenSSH should be able to work with most implementations, but take into consideration that some of the older protocols or encryption tools might be disabled in the newer releases.
To ensure a high-security level, OpenSSH comes with support for strong encryption algorithms, such as AES, RSA, ECDSA, ChaCha20, Ed25519, and more. Since OpenSSH makes sure that the encryption is active right from the start, all your credentials are protected at all times.
OpenSSH also delivers robust authentication tools, such as one-time passwords or public keys, which is great if you want to protect yourself against spoofing practices. The port forwarding capabilities permit you to establish TCP/IP connections by using an encrypted channel.
Bottom line, OpenSSH enables you to rely on the latest SSH standards to make sure that you are establishing connections to remote computers or transfer files without compromising on security.
OpenSSH helps you create encrypted tunnels by relying on strong algorithms, delivers strong authentication tools, and can deal with applications that require internet access yet take an insecure approach.
What's new in OpenSSH 9.6:
- This release contains a number of security fixes, some small features and bugfixes.
- Security:
OpenSSH 9.6
add to watchlist add to download basket send us an update REPORT- runs on:
- macOS (-)
- file size:
- 941 KB
- filename:
- openssh-9.6.tar.gz
- main category:
- Network/Admin
- developer:
- visit homepage
Windows Sandbox Launcher
ShareX
IrfanView
Microsoft Teams
Zoom Client
7-Zip
Context Menu Manager
4k Video Downloader
calibre
Bitdefender Antivirus Free
- 4k Video Downloader
- calibre
- Bitdefender Antivirus Free
- Windows Sandbox Launcher
- ShareX
- IrfanView
- Microsoft Teams
- Zoom Client
- 7-Zip
- Context Menu Manager