A CLI based SQL injection web scanner. #SQL injection #Web scanner #Identify SQL vulnerability #SQL #Injection #Web
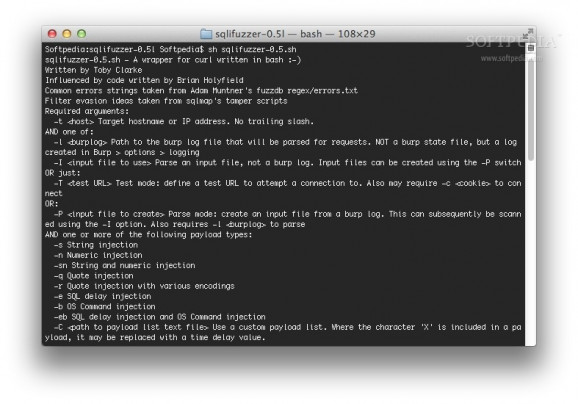
sqlifuzzer is a free and open-source command line scanner that was designed to identify SQL injection vulnerabilities. It parses Burp logs to create a list of fuzzable requests, then fuzzes them.
More specifically, sqlifuzzer is a wrapper for curl written in bash. sqlifuzzer is also a tool that can be used to remotely identify SQL (and XPath) injection vulnerabilities. It does this by sending a range of injection payloads and examining the responses for signs of 'injectability'. If a parameter is vulnerable, sqlifuzzer sends exploit payloads to extract data.
Note that sqlifuzzer is beta, so don't use it in an environment that matters to you or anyone else. Also, do not use sqlifuzzer to scan hosts without the owner's permission.
sqlifuzzer is cross-platform and it works on Mac OS X, Windows and Linux.
Detailed instructions on how to install and use the sqlifuzzer utility on your Mac are available HERE.
What's new in sqlifuzzer 0.6:
- Fixed a bug preventing time based exploitation from being triggered.
sqlifuzzer 0.6
add to watchlist add to download basket send us an update REPORT- runs on:
- Mac OS X (-)
- file size:
- 63 KB
- main category:
- Developer Tools
- developer:
- visit homepage
Zoom Client
Microsoft Teams
4k Video Downloader
IrfanView
Bitdefender Antivirus Free
7-Zip
ShareX
paint.net
Windows Sandbox Launcher
calibre
- paint.net
- Windows Sandbox Launcher
- calibre
- Zoom Client
- Microsoft Teams
- 4k Video Downloader
- IrfanView
- Bitdefender Antivirus Free
- 7-Zip
- ShareX